Trust Model for Underwater Wireless Sensor Networks Based on Variational Autoencoders
-
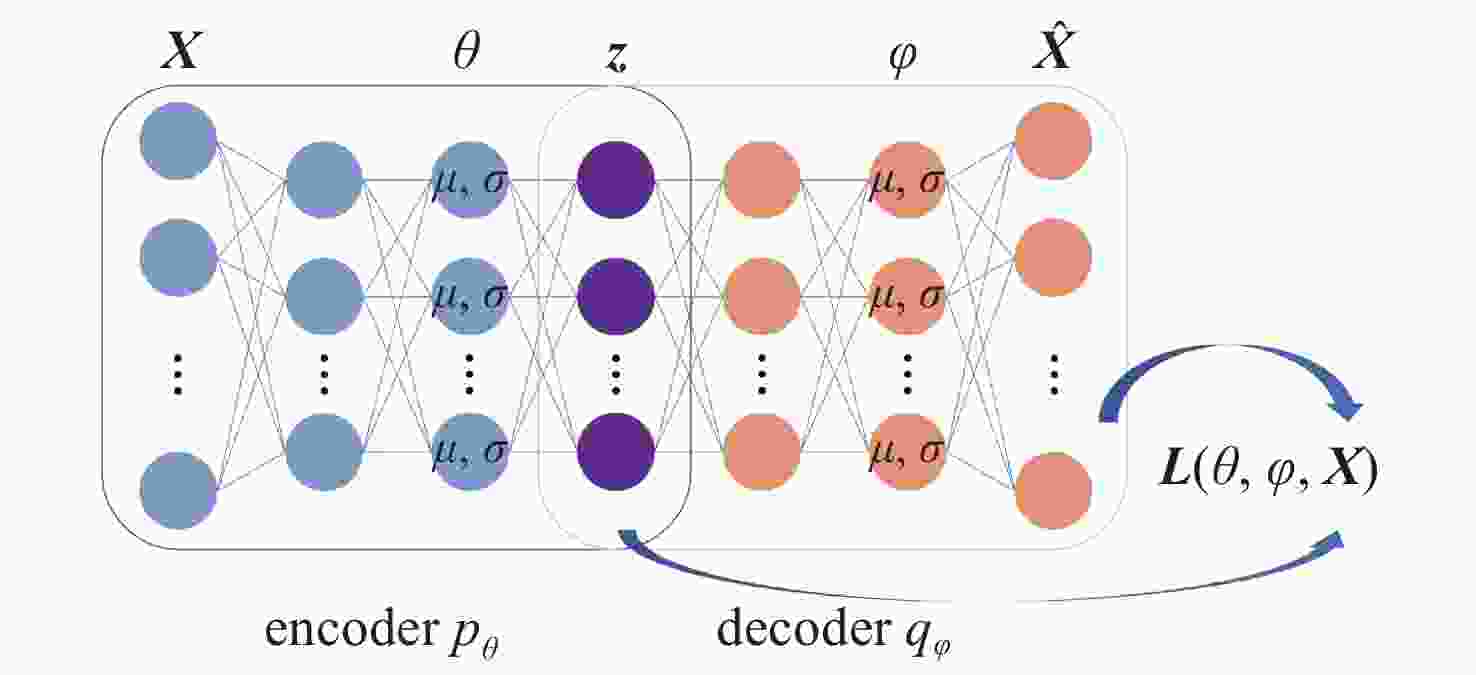
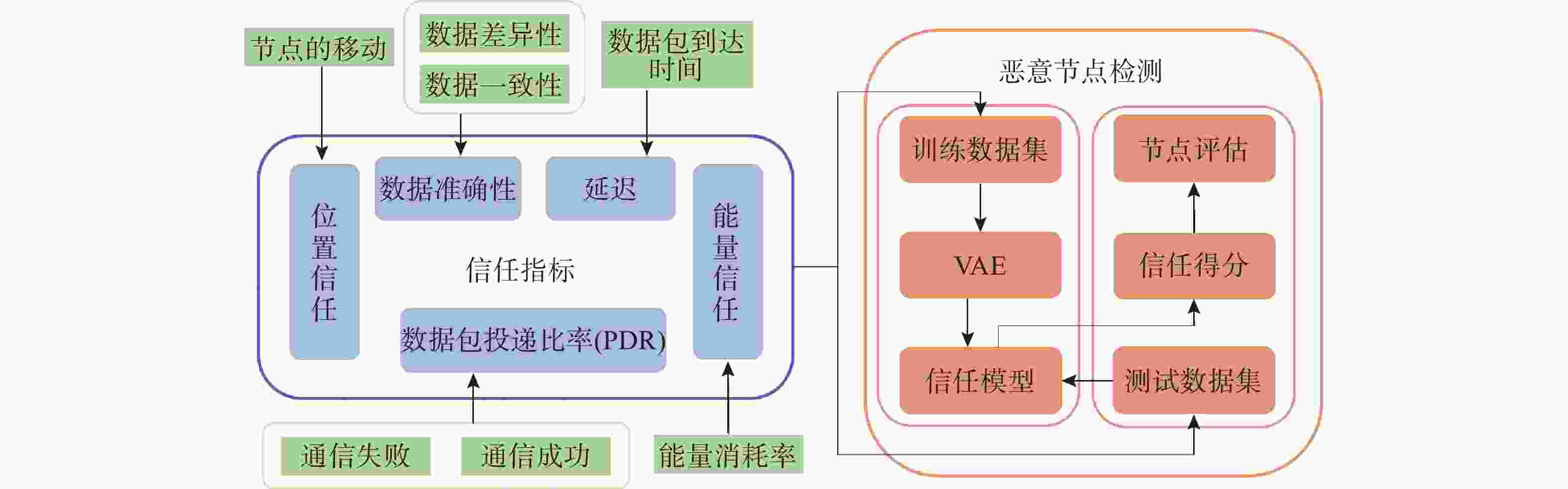
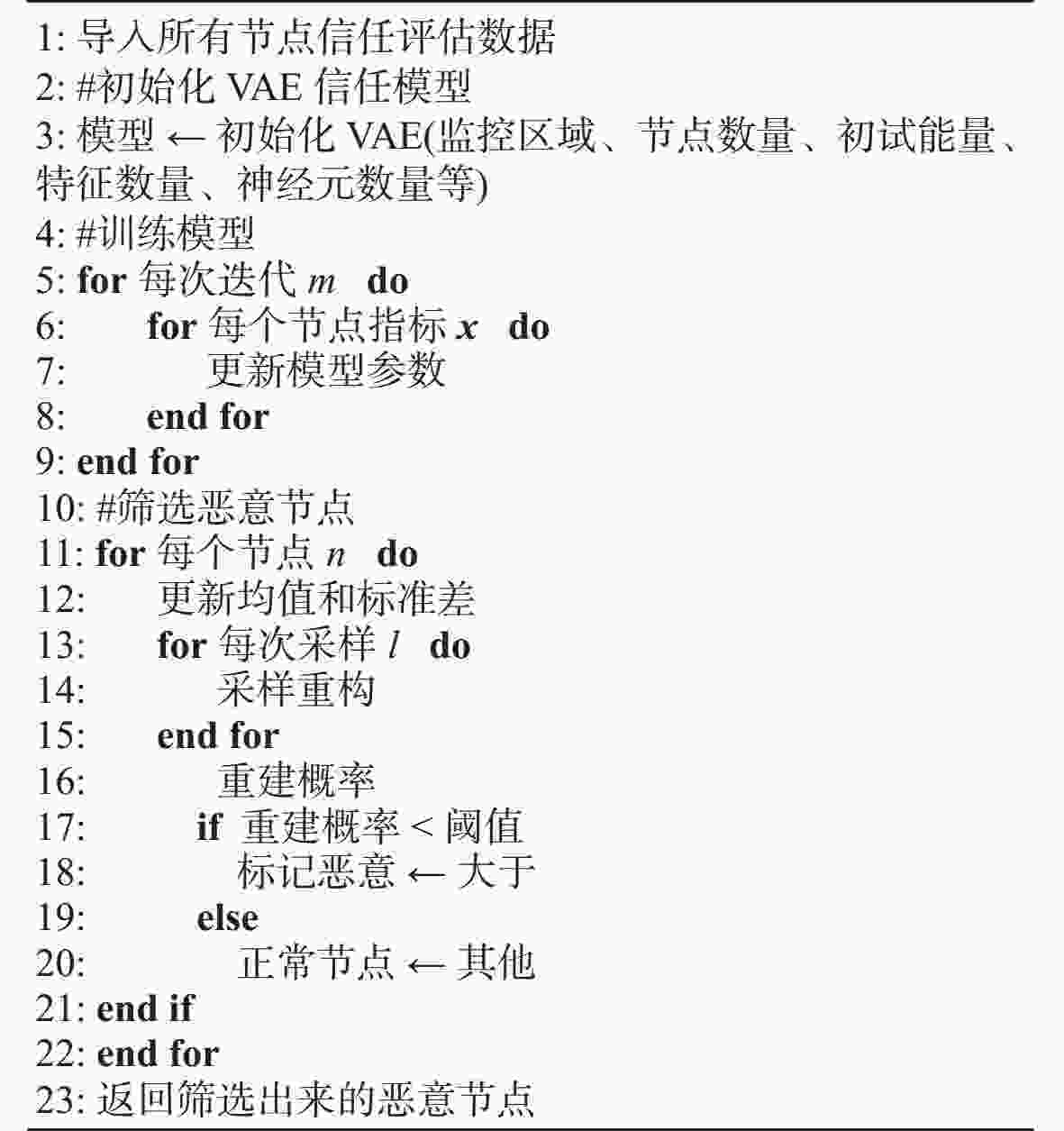
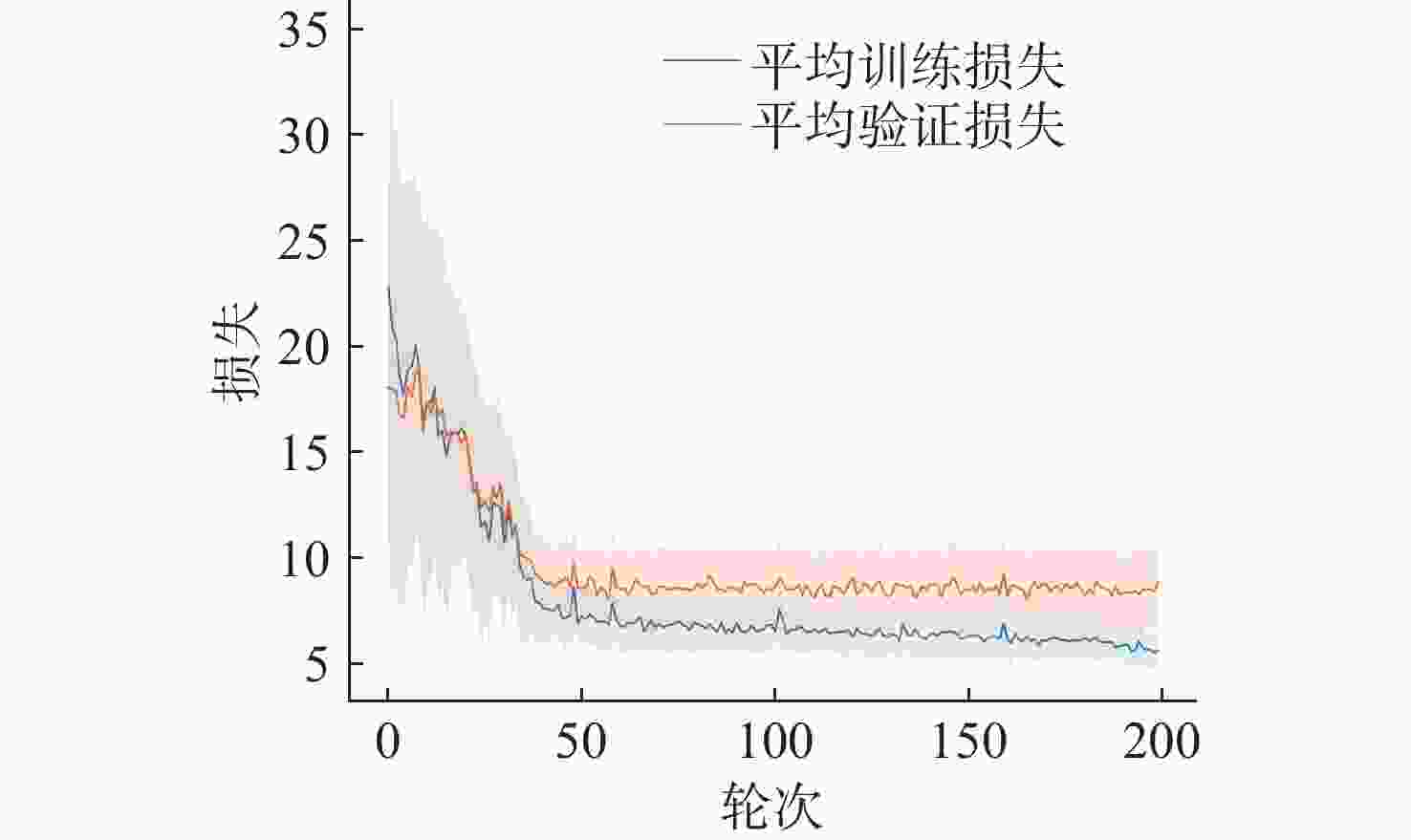
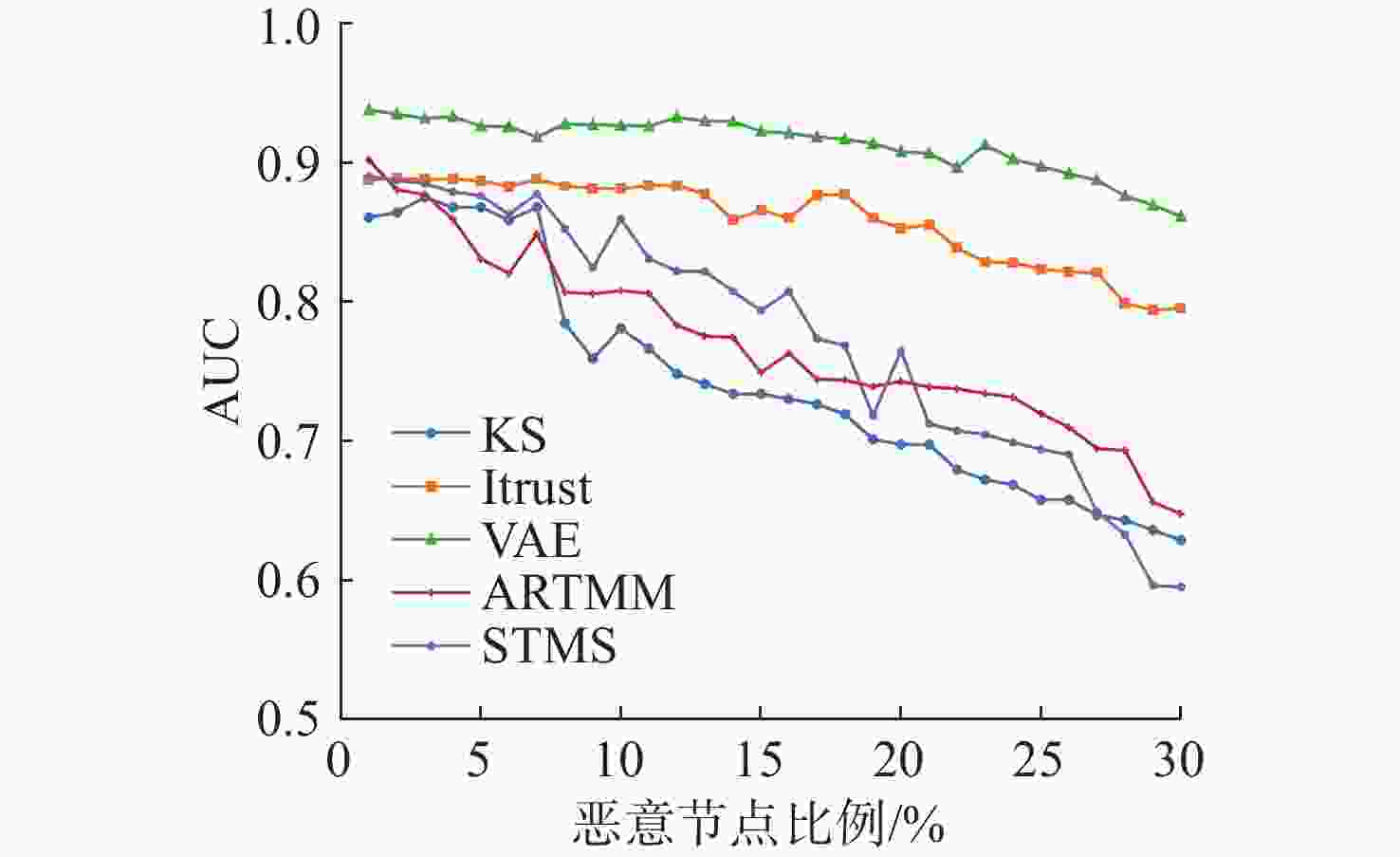
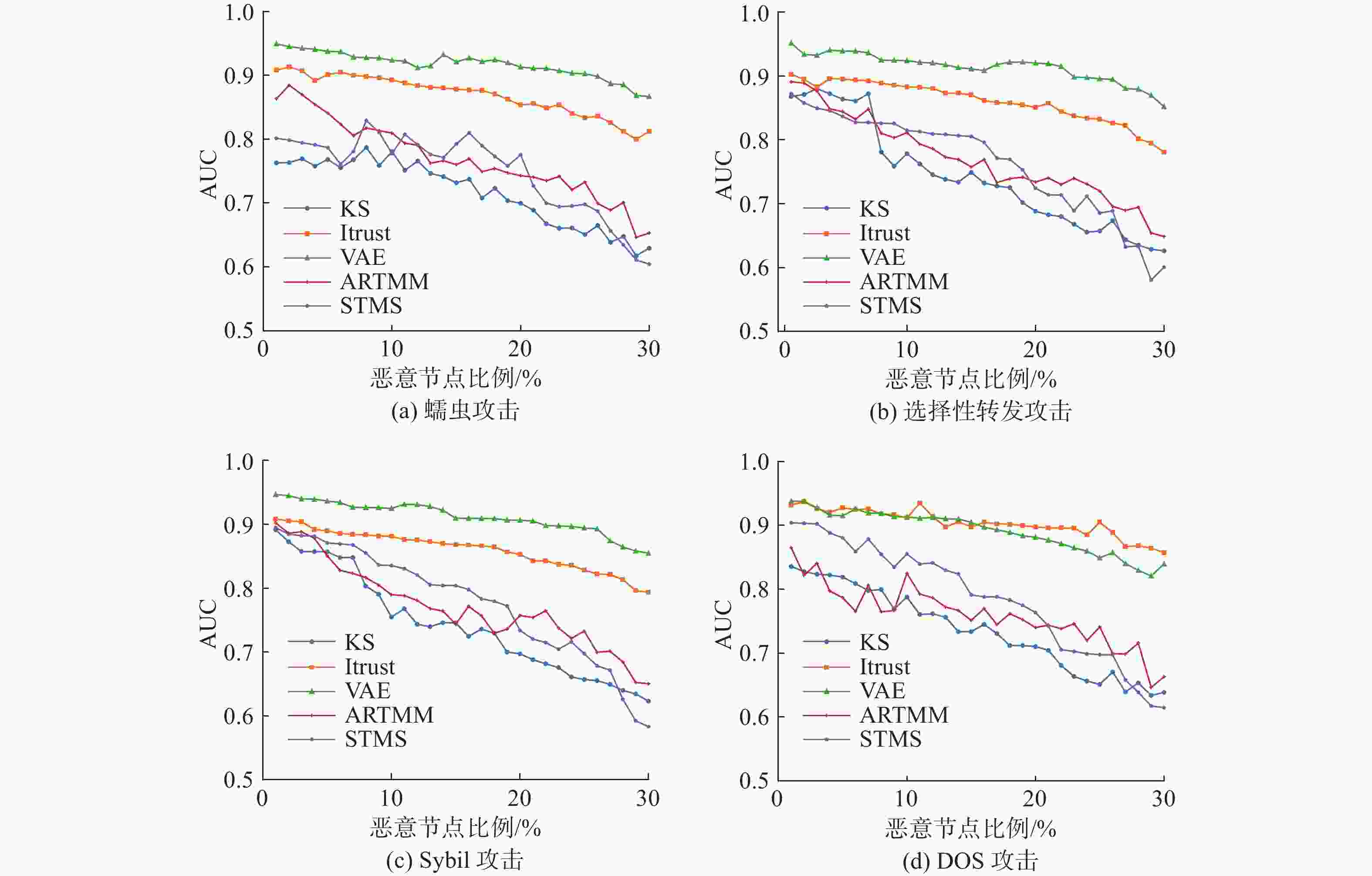
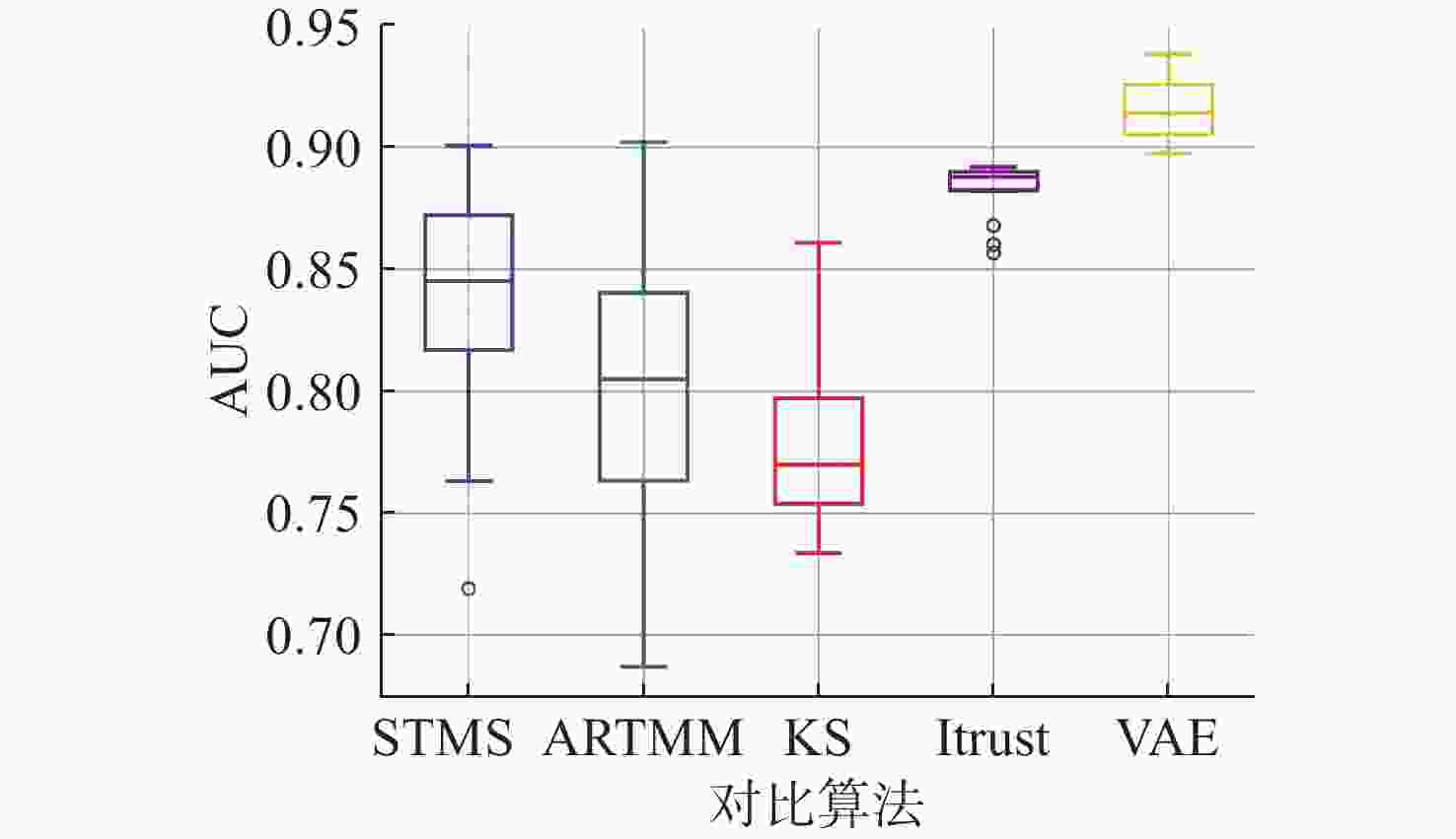
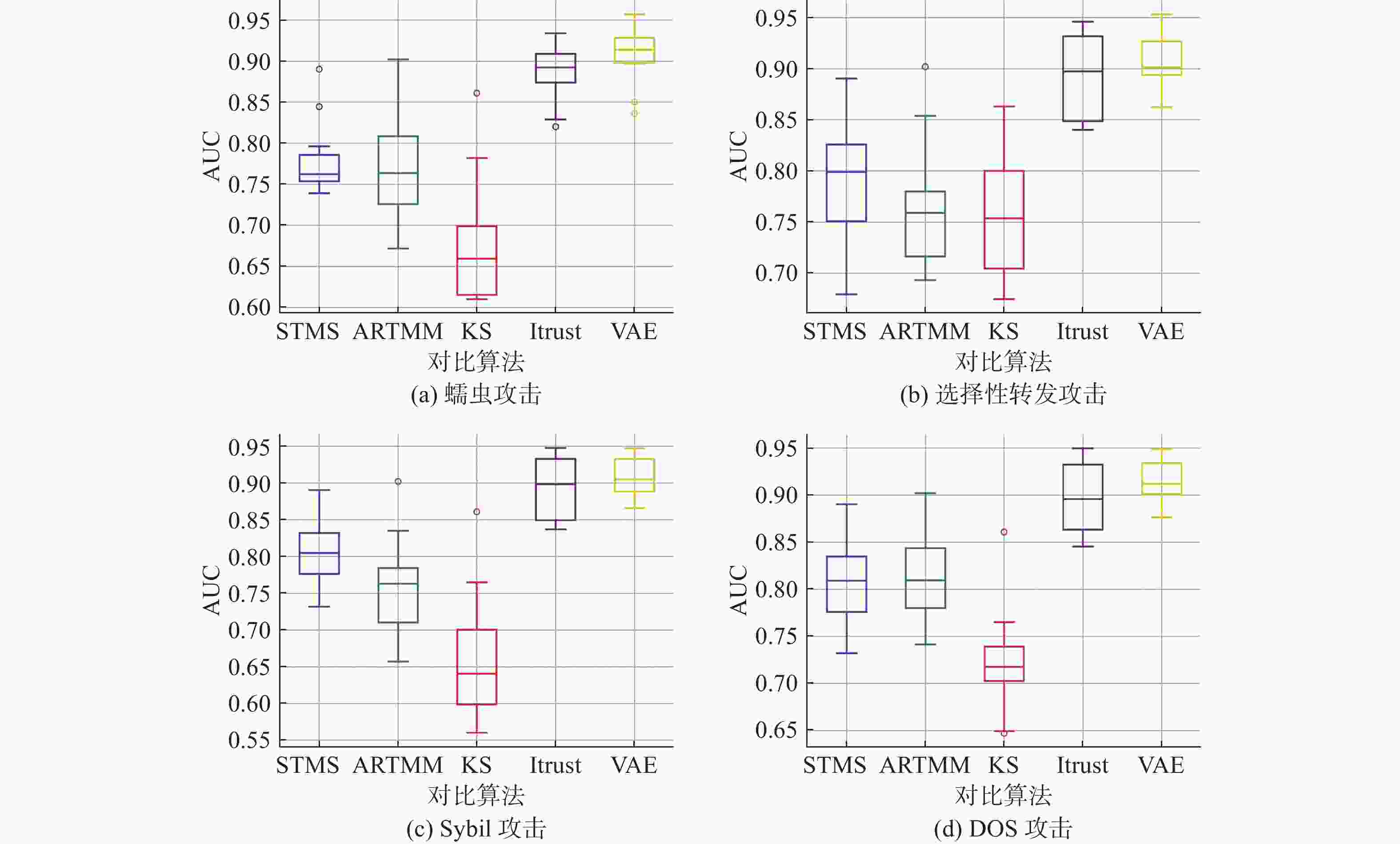
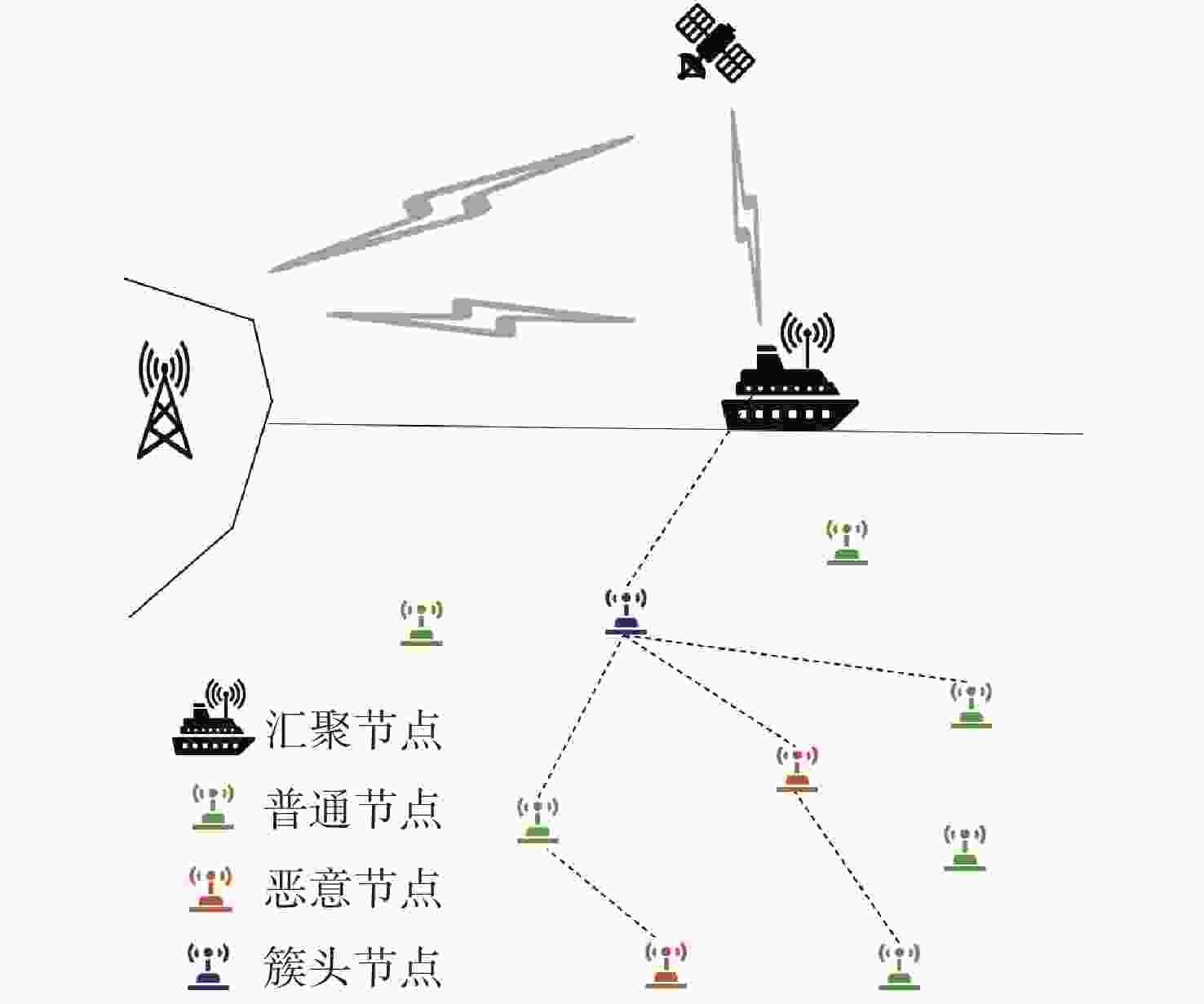
摘要: 在水下无线传感器网络(UWSN)中, 复杂的水声通信环境与受限的节点资源使恶意节点的攻击更具隐蔽性和威胁性, 因此研究有效的恶意节点检测方法对维护网络稳定与数据安全至关重要。文中提出了一种基于变分自动编码器的UWSN信任模型, 通过评估节点行为可信度来判定其是否为恶意节点。首先由汇聚节点收集水下节点传输过程中的行为特征数据, 从中提取位置、数据包投递比率及延迟等指标, 构成信任数据集; 然后对数据集进行编码训练, 利用变分推理将数据映射到潜在空间, 并获得该空间的概率分布; 最后依据概率分布解码重构数据, 得到节点行为可信度, 从而完成对节点的信任评估。对比实验结果表明, 相较于基于入侵检测的信任管理系统等方法, 该模型在信任评估准确度方面至少提升了10.5%, 同时在运行稳定性方面也具有明显的优势。Abstract: In underwater wireless sensor networks(UWSNs), the complex underwater acoustic communication environment and the limited resources of nodes make malicious node attacks more covert and threatening. Therefore, researching effective malicious node detection methods is crucial for maintaining network stability and data security. This paper proposed a trust model for UWSNs based on variational autoencoders(VAEs), which evaluated node behavior credibility to identify malicious nodes. First, the model aggregated the behavioral feature data from the underwater node transmission process, extracting various indicators such as node location, packet delivery ratio, and delay, thereby forming a trust dataset. The dataset was then encoded and trained, and variational inference was employed to map the data to a latent space and obtain the probability distribution of this space. Finally, based on the probability distribution, the model decoded and reconstructed the data to derive node behavior credibility, thus completing the trust evaluation of nodes. Comparative experimental results show that compared to methods such as the intrusion detection-based trust management system, the proposed model improves trust evaluation accuracy by at least 10.5% and demonstrates significant advantages in operational stability.
-
Key words:
- underwater wireless sensor network /
- trust model /
- variational autoencoder
-
表 1 VAE的参数列表
Table 1. Parameter list of VAE
参数 设置 监控区域 500 m×500 m×500 m 节点数量 200 初始能量/J 1 000 特征数量 5 神经元数量 64, 64 潜在空间纬度 2 隐藏层激活函数 ReLU 输出层激活函数 Sigmoid 优化器 Adam 迭代次数 300 表 2 VAE信任模型检测性能结果
Table 2. Detection performance results of the VAE trust model
节点
个数恶意节
点比例AUC 真阴性
(TN)真阳性
(TP)假阴性
(FN)假阳性
(FP)50 0.1 0.94 43±1 4±1 1±1 1±1 0.2 0.92 38±2 8±1 2±2 2±1 0.3 0.89 33±2 13±1 2±2 2±1 100 0.1 0.94 89±1 9±1 1±1 1±1 0.2 0.93 78±2 18±2 2±2 2±2 0.3 0.89 65±3 26±2 4±3 3±2 200 0.1 0.94 176±3 16±2 3±3 3±2 0.2 0.90 154±4 34±3 5±4 5±3 0.3 0.88 131±3 52±3 7±3 7±3 -
[1] YAN J, MENG Y, YANG X, et al. Privacy-preserving localization for underwater sensor networks via deep reinforcement learning[J]. IEEE Transactions on Information Forensics and Security, 2020, 16: 1880-1895. [2] El-RABAIE S, NABIL D, MAHMOUD R, et al. Underwater wireless sensor networks(UWSN), architecture, routing protocols, simulation and modeling tools, localization, security issues and some novel trends[J]. Network Communications Engineering, 2015, 7(8): 335-354. [3] HAN G, JIANG J, SUN N, et al. Secure communication for underwater acoustic sensor networks[J]. IEEE Communications Magazine, 2015, 53(8): 54-60. doi: 10.1109/MCOM.2015.7180508 [4] DAS A, ISLAM M M. SecuredTrust: A dynamic trust computation model for secured communication in multiagent systems[J]. IEEE Transactions on Dependable and Secure Computing, 2011, 9(2): 261-274. [5] CHO J, CHEN R. PROVEST: Provenance-based trust model for delay tolerant networks[J]. IEEE Transactions on Dependable and Secure Computing, 2016, 15(1): 151-165. [6] SHAHAPUR S, KHANAI R. Localization, routing and its security in UWSN—A survey[C]//2016 International Conference on Electrical, Electronics, and Optimization Techniques(ICEEOT). Tamil Nadu, India: IEEE, 2016: 1001-1006. [7] HAN G, JIANG J, SHU L, et al. An attack-resistant trust model based on multidimensional trust metrics in underwater acoustic sensor network[J]. IEEE Transactions on Mobile Computing, 2015, 14(12): 2447-2459. doi: 10.1109/TMC.2015.2402120 [8] JIANG J, HAN G, ZHU C, et al. A trust cloud model for underwater wireless sensor networks[J]. IEEE Communications Magazine, 2017, 55(3): 110-116. doi: 10.1109/MCOM.2017.1600502CM [9] DU J, HAN G, LIN C, et al. ITrust: An anomaly-resilient trust model based on isolation forest for underwater acoustic sensor networks[J]. IEEE Transactions on Mobile Computing, 2020, 21(5): 1684-1696. [10] DU J X, HAN G J, LIN C, et al. LTrust: An adaptive trust model based on LSTM for underwater acoustic sensor networks[J]. IEEE Transactions on Wireless Communications, 2022, 21(9): 7314-7328. doi: 10.1109/TWC.2022.3157621 [11] HAN G, HE Y, JIANG J, et al. Fault-tolerant trust model for hybrid attack mode in underwater acoustic sensor networks[J]. IEEE Network, 2020, 34(5): 330-336. doi: 10.1109/MNET.001.2000006 [12] JIANG B, ZHOU R, LUO F, et al. Hybrid trust model for identifying malicious attacks in underwater acoustic sensor network[J]. IEEE Sensors Journal, 2024, 24(6): 26743-26754. [13] WANG B, YUE X, LIU Y, et al. A dynamic trust model for underwater sensor networks fusing deep reinforcement learning and random forest algorithm[J]. Applied Sciences, 2024, 14(8): 3374. doi: 10.3390/app14083374 [14] DAI L, LIN T, LIU C, et al. Sdfvae: Static and dynamic factorized VAE for anomaly detection of multivariate CDN KPIs[C]//Proceedings of the Web Conference 2021. Ljubljana, Slovenia: WC, 2021: 3076-3086. [15] YISA A, DARGAHI T, BELGUITH S, et al. Security challenges of internet of underwater things: A systematic literature review[J]. Transactions on Emerging Telecommunications Technologies, 2021, 32(3): e4203. [16] TSAI D, JEN P. Autoencoder-based anomaly detection for surface defect inspection[J]. Advanced Engineering Informatics, 2021, 48: 101272. doi: 10.1016/j.aei.2021.101272 [17] LIN S, CLARK R, BIRKE R, et al. Anomaly detection for time series using vae-lstm hybrid model[C]//ICASSP 2020-2020 IEEE International Conference on Acoustics, Speech and Signal Processing(ICASSP). Barcelona, Spain: IEEE, 2020: 4322-4326. [18] KHAN Z, GANG Q, MUHAMMAD A, et al. A comprehensive survey of energy-efficient MAC and routing protocols for underwater wireless sensor networks[J]. Electronics, 2022, 11(19): 3015. doi: 10.3390/electronics11193015 [19] XIA N, DU H, LI S, et al. VSPSA for acoustic source localization in wireless sensor networks[J]. Adhoc & Sensor Wireless Networks, 2013, 19(3-4): 277-304. [20] DIAMANT R, CASARI P, TOMANSIN S. Cooperative authentication in underwater acoustic sensor networks[J]. IEEE Transactions on Wireless Communications, 2018, 18(2): 954-968. [21] GUQHAIMAN A, AKANBI O, ALJADI A, et al. A survey on MAC protocol approaches for underwater wireless sensor networks[J]. IEEE Sensors Journal, 2020, 21(3): 3916-3932. [22] HAN G, HE Y, JIANG J, et al. A synergetic trust model based on SVM in underwater acoustic sensor networks[J]. IEEE Transactions on Vehicular Technology, 2019, 68(11): 11239-11247. doi: 10.1109/TVT.2019.2939179 [23] JAYASINGHE U, LEE G, UM T, et al. Machine learning based trust computational model for IoT services[J]. IEEE Transactions on Sustainable Computing, 2018, 4(1): 39-52. -




 下载:
下载: